Integrating Chromebook Management
Configuring the Google Service Account
Log into Google Cloud Platform https://console.cloud.google.com/
From the top menu select the drop-down box to the right of Cloud Platform and select one of the existing projects
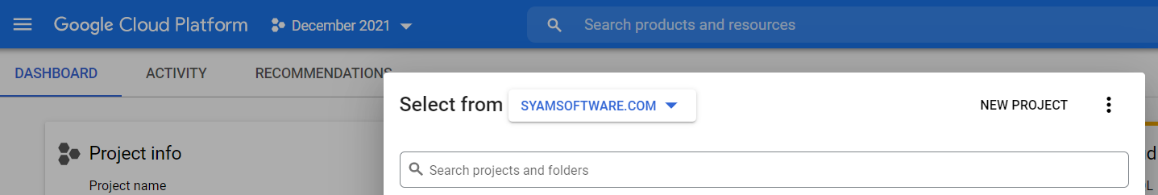
Click New Project
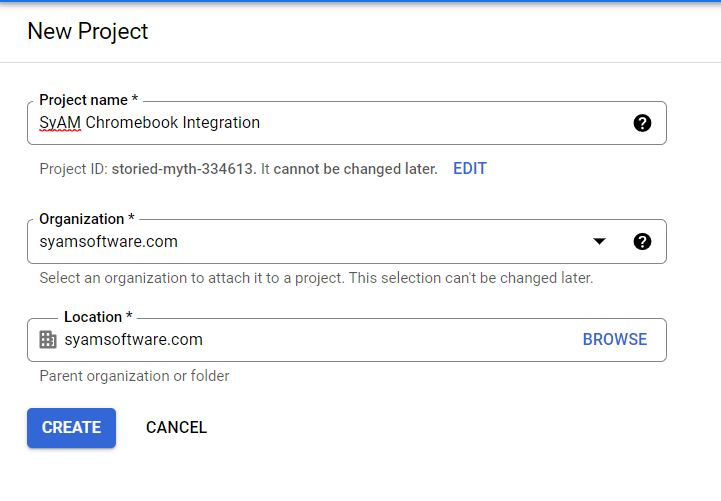
Give the Project a name and click Create
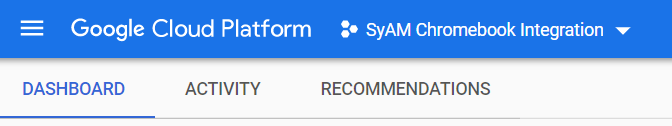
This will take you back to the Dashboard
Now select the new project from the drop down next to Cloud
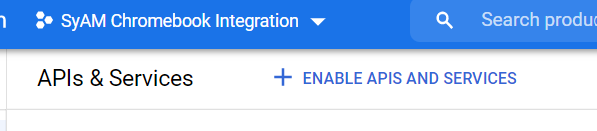
Scroll down the page and under Getting Started select API Explore and enable APIs
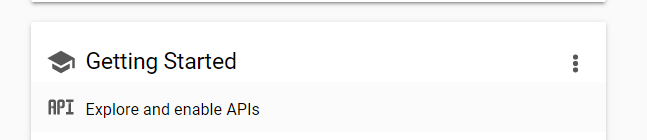
Now click on enable APIs
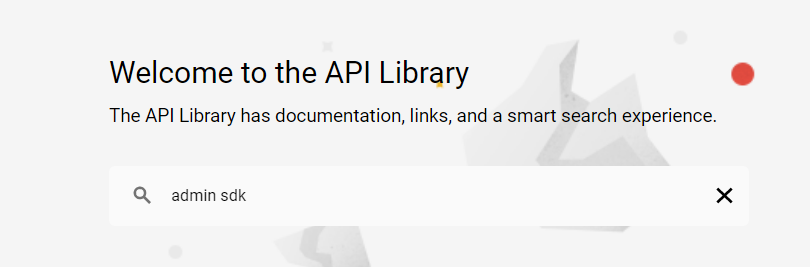
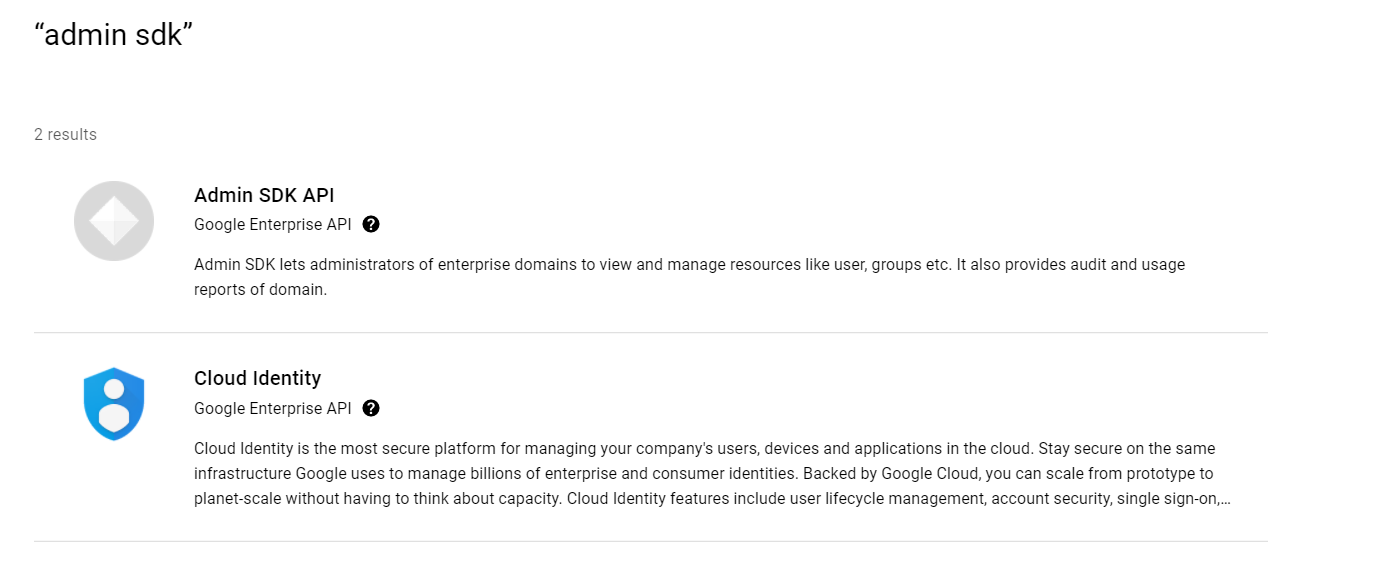
Enter admin sdk in the search box
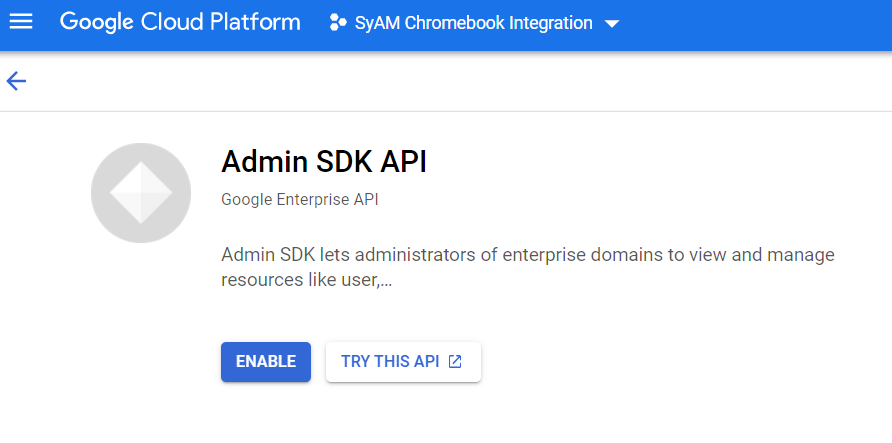
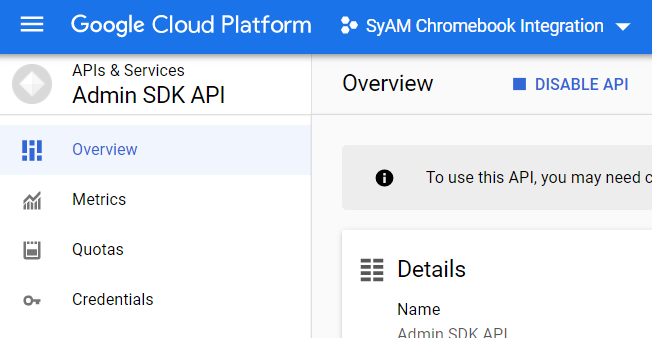
Select Admin SDK API
Click Enable
Now select Credentials from the left menu
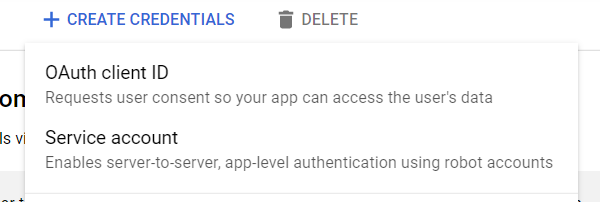
Click Create Credentials
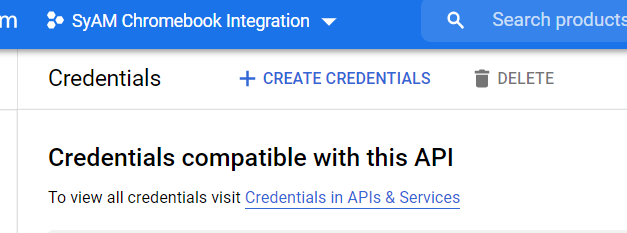
Select Service Account
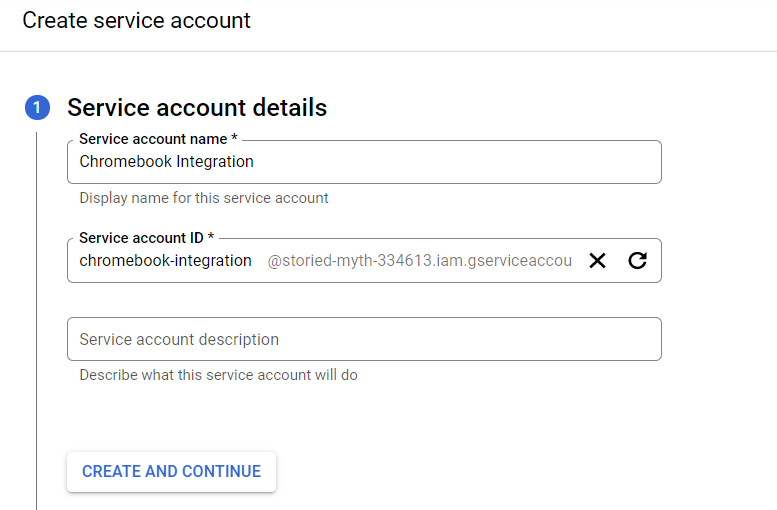
Give the service account a name and click Create and Continue
Under Roles select Currently Used – Owner then click to continue
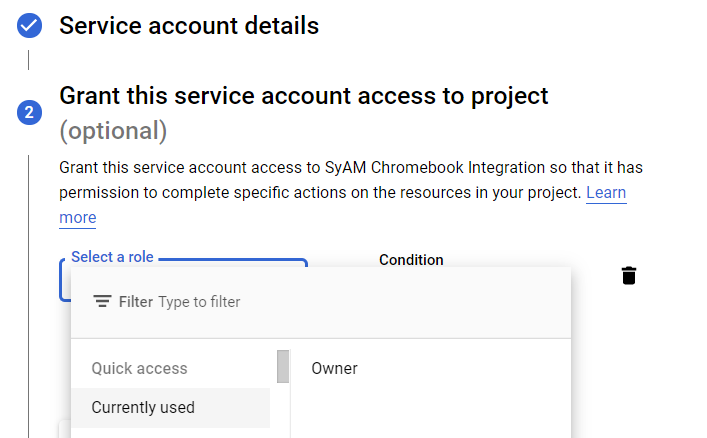
Leave the Grant User access to this service account empty, press Done
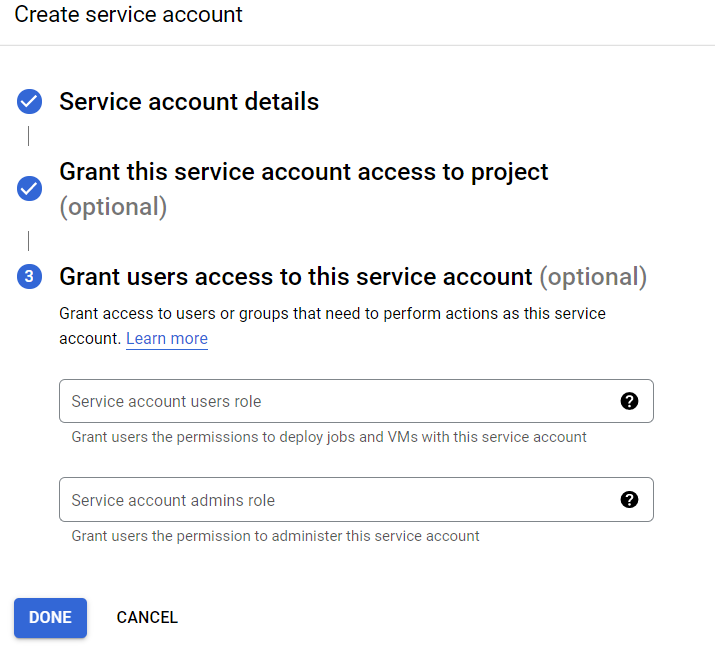
Once back at the Credentials Menu click on the service account
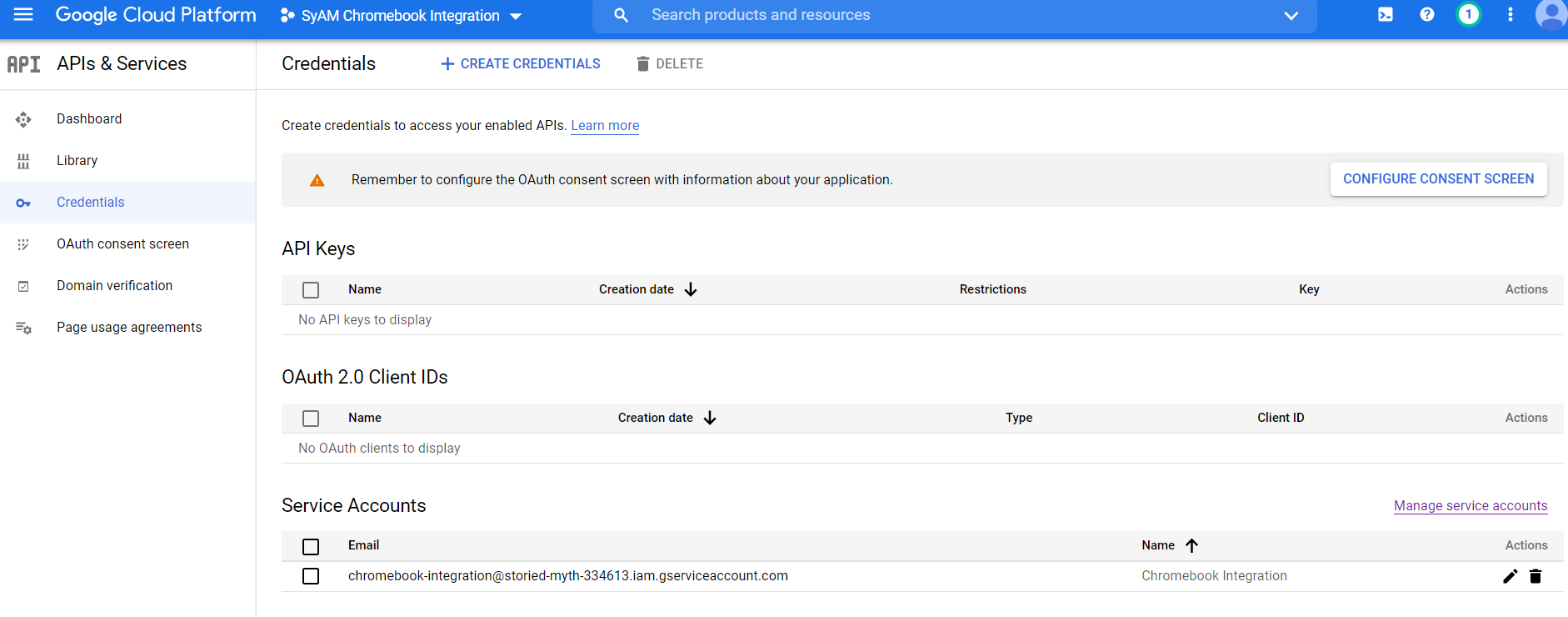
Copy the email and unique id to notepad as we need to paste this data into the SyAM MDM.
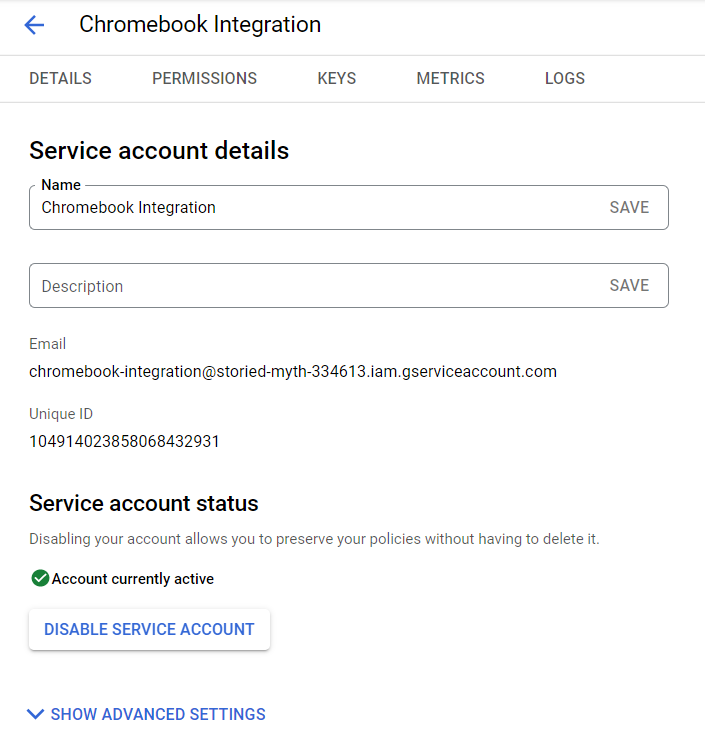
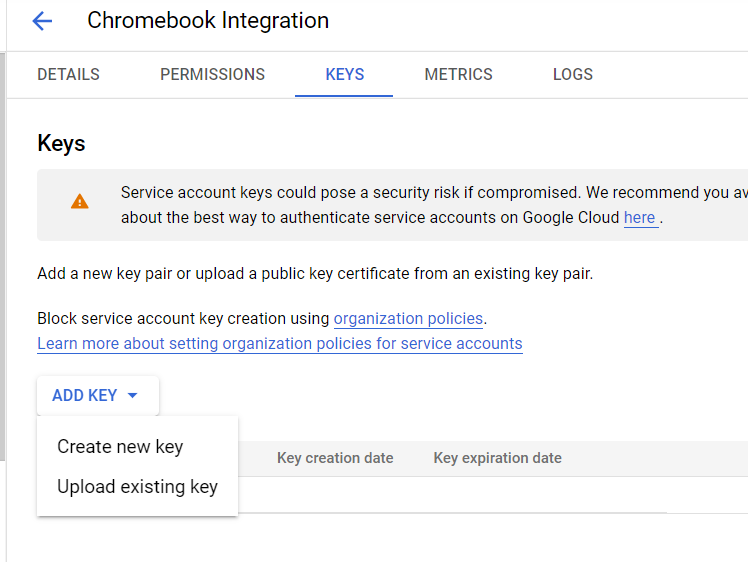
Click on Keys and then select Create New Key
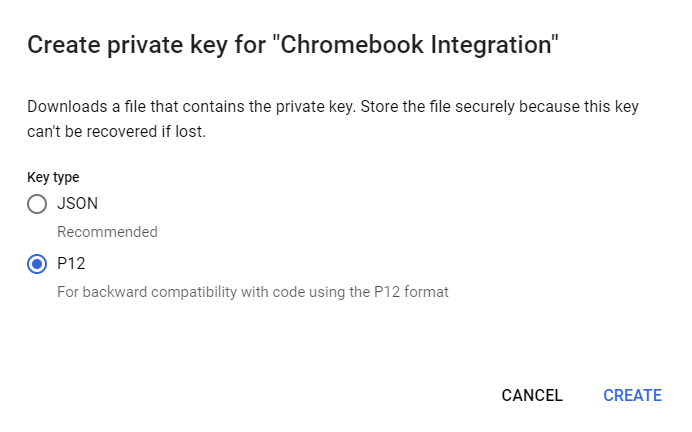
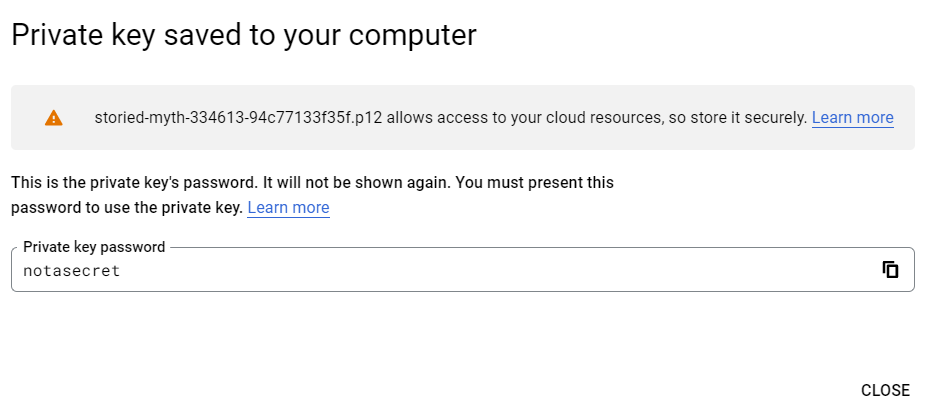
Select P12 and Create the key file
Press Close and it will save the file, you will need to upload this into the SyAM MDM
You can now log out of the Google Cloud Platform.
Update the Google Admin Console
Next we need to enable this new service account in Google Admin Console.
Login to your Google Apps Admin console. https://admin.google.com
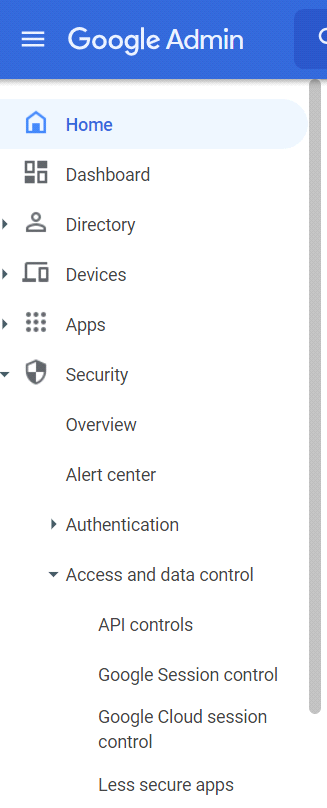
Expand Security – Access and data control from the left menu and select API controls
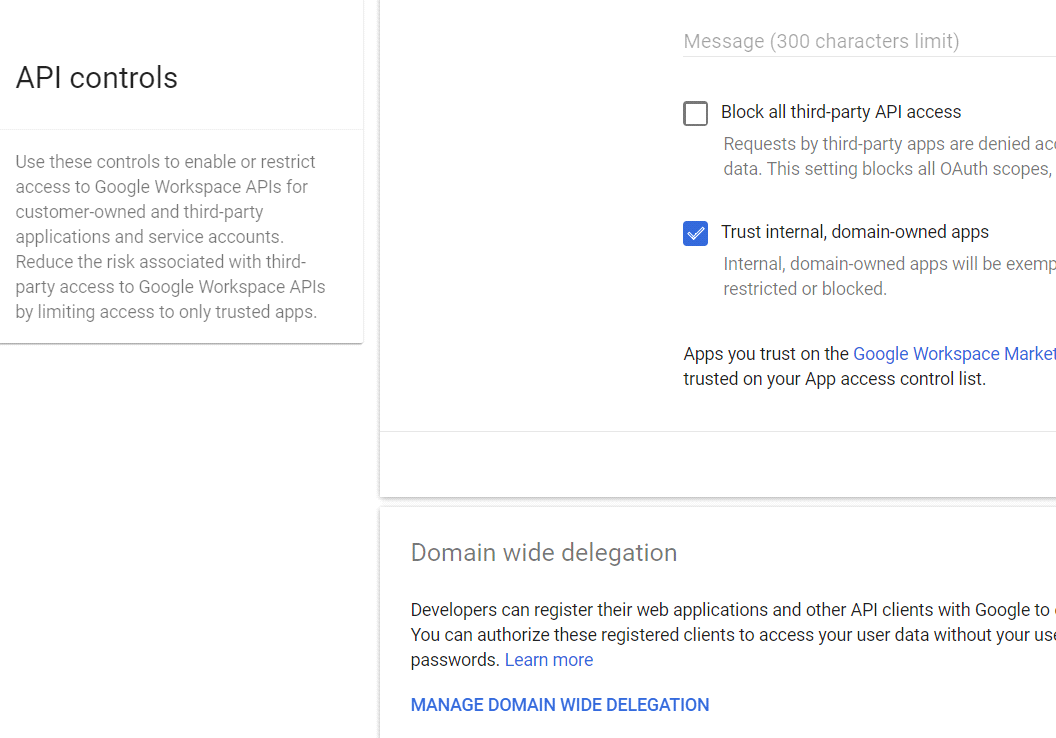
Scroll down the page and select Manage Domain Wide Delegation
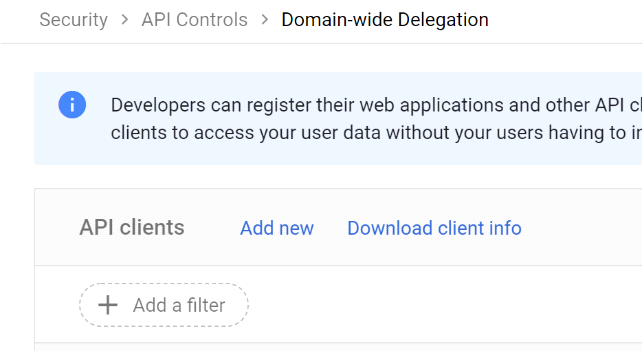
Click Add New
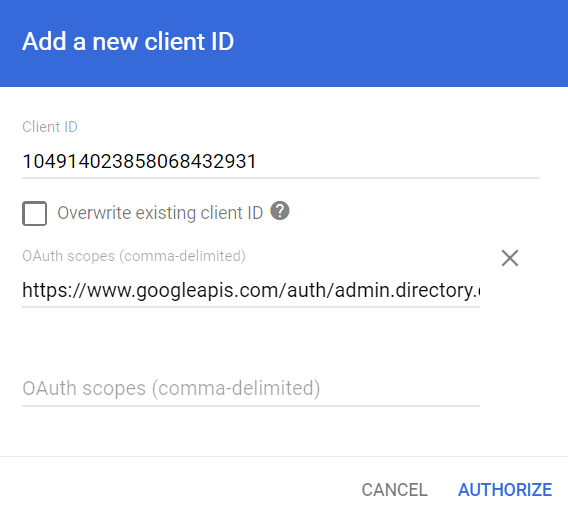
Select Manage API client access in the Authentication section. In the Client Name field enter the service account's Client ID. (This is the Unique ID from the Service Account Details we had pasted into notepad)
Paste in the following under OAuth scopes
https://www.googleapis.com/auth/admin.directory.device.chromeos, https://www.googleapis.com/auth/admin.directory.group.member, https://www.googleapis.com/auth/admin.directory.user, https://www.googleapis.com/auth/admin.directory.orgunit, https://www.googleapis.com/auth/admin.directory.group, https://www.googleapis.com/auth/apps.licensing, https://www.googleapis.com/auth/chromewebstore.readonly,https://www.googleapis.com/auth/admin.reports.audit.readonly, https://www.googleapis.com/auth/admin.reports.usage.readonly,https://www.googleapis.com/auth/admin.directory.rolemanagement,https://www.googleapis.com/auth/admin.directory.userschema,https://www.googleapis.com/auth/classroom.courses, https://www.googleapis.com/auth/classroom.rosters
Then Click Authorize
Log out of Google Admin Console
Log into the SyAM MDM Interface
Click on the left menu Managed Devices – select ChromeOS
Upload the P12 file and paste in the ID and email from your Service Account Details
Press Next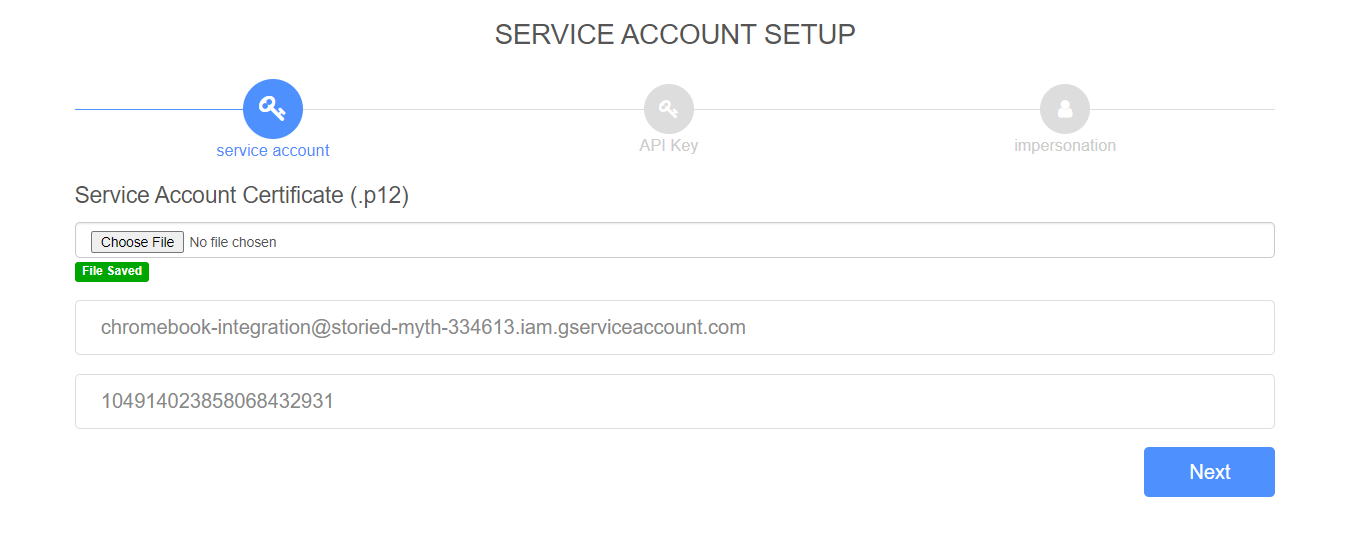
Skip the key for Static Maps by pressing Next
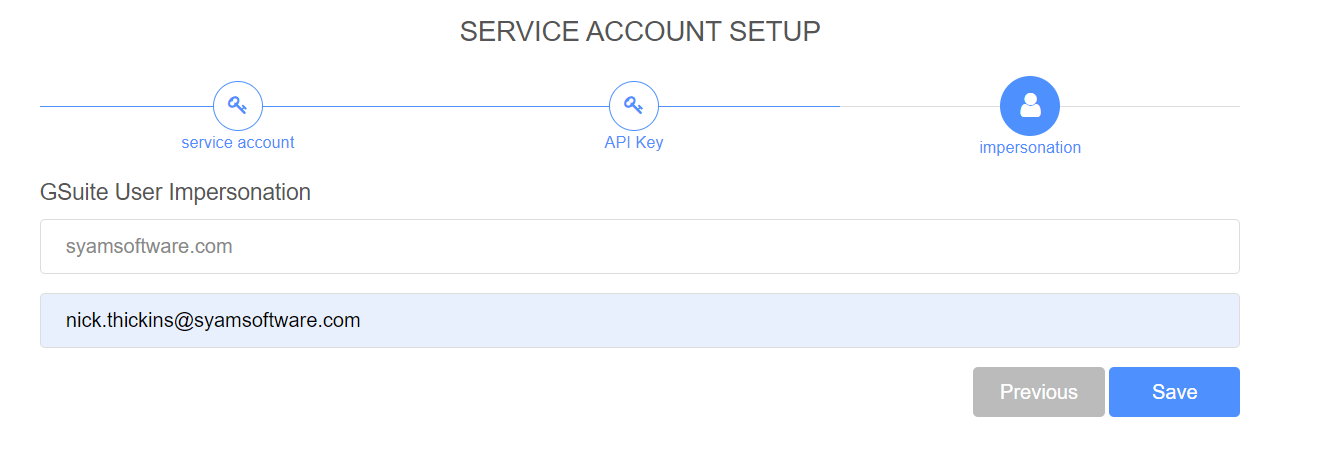
Enter the domain and the user email address that was used to Authorize the Service API in Google Admin Console and press Save
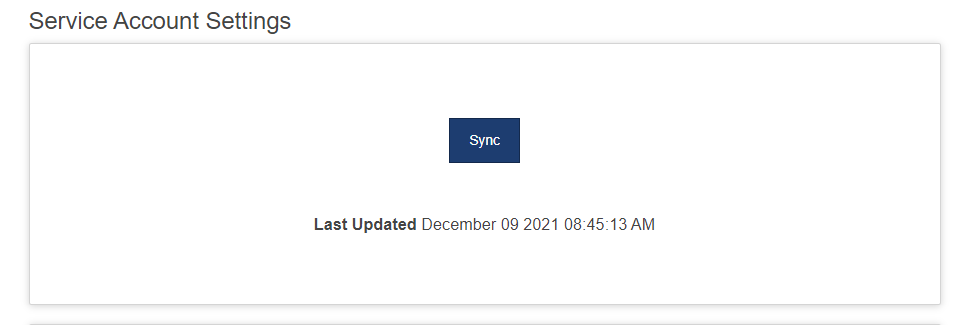
Press Sync
After it completes the Sync, it will present that data retrieved from Google.
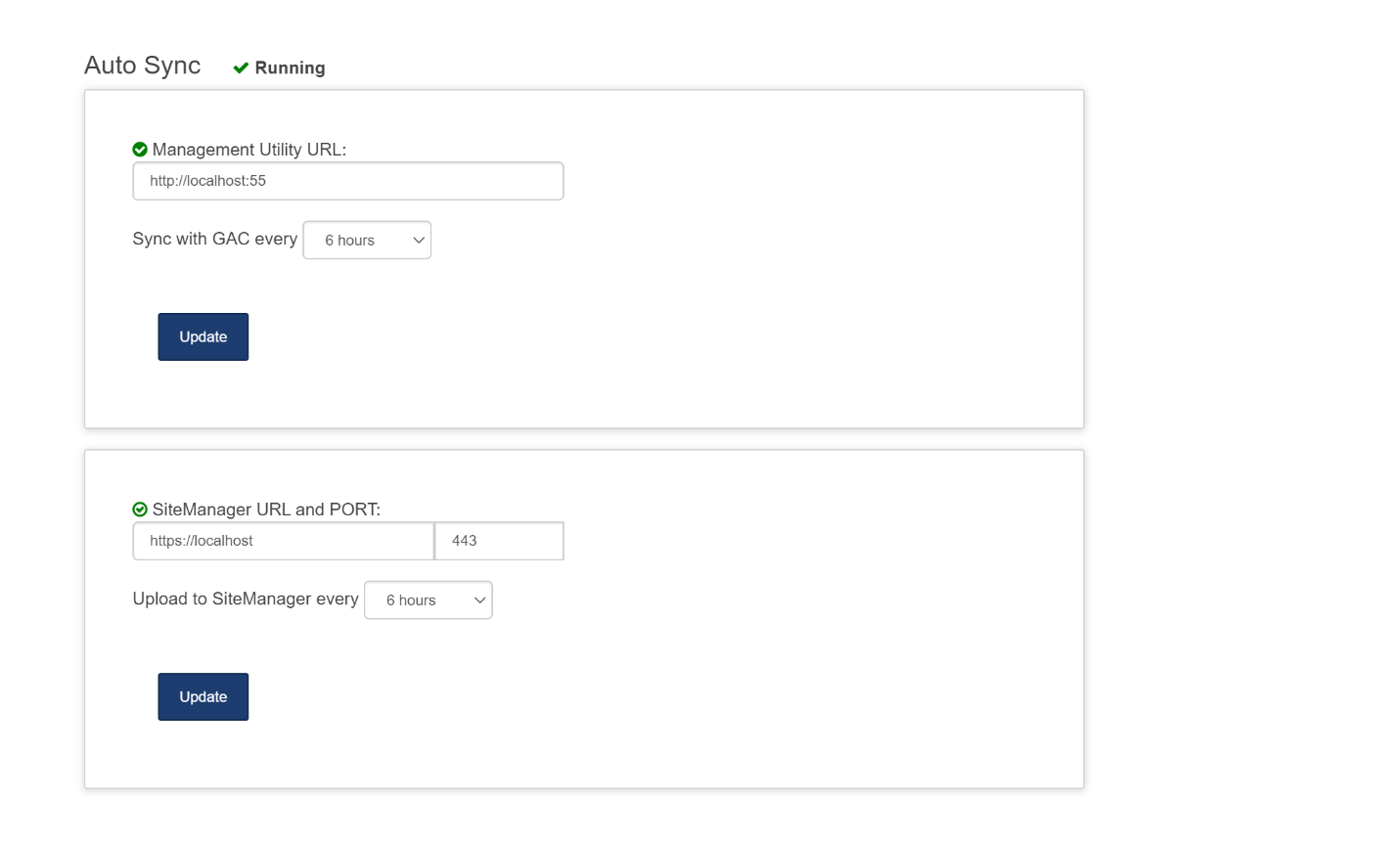
You can now set the Polling Interval for the GAC Sync and the Site Manager Asset Update
Possible reasons why the error Authorization Status 401 Unauthorized can occur
Incorrect Role chose for the service account – it must be set to Project – Service Account Actor
- To resolve, delete the two sets of settings in the Chrome OS page in Management Utilities, delete the service account and start the process again, creating a new service account and then add the new service account into Google Admin Console with the URLs.
Incorrect Google Apps Email Address, possibly a typo or the email account used was not the account used when logging into Google Admin Console to add in the URLs to the Service account.
- To resolve delete the Google Apps Domain information in the Chrome OS page in Management Utilities, then enter the correct email address and press save.
Likely reason the error Authorization Status 403 Unauthorized can occur
Service Account Created but the API was not enabled
To resolve, log back into the Google Cloud, https://console.cloud.google.com/ select your project and click to enable APIs